“Astelia gives us the network context needed to understand which vulnerabilities actually matter in our environment, so we can prioritize based on real exposure, not just raw scores.”

Ben Bachmann, CISO

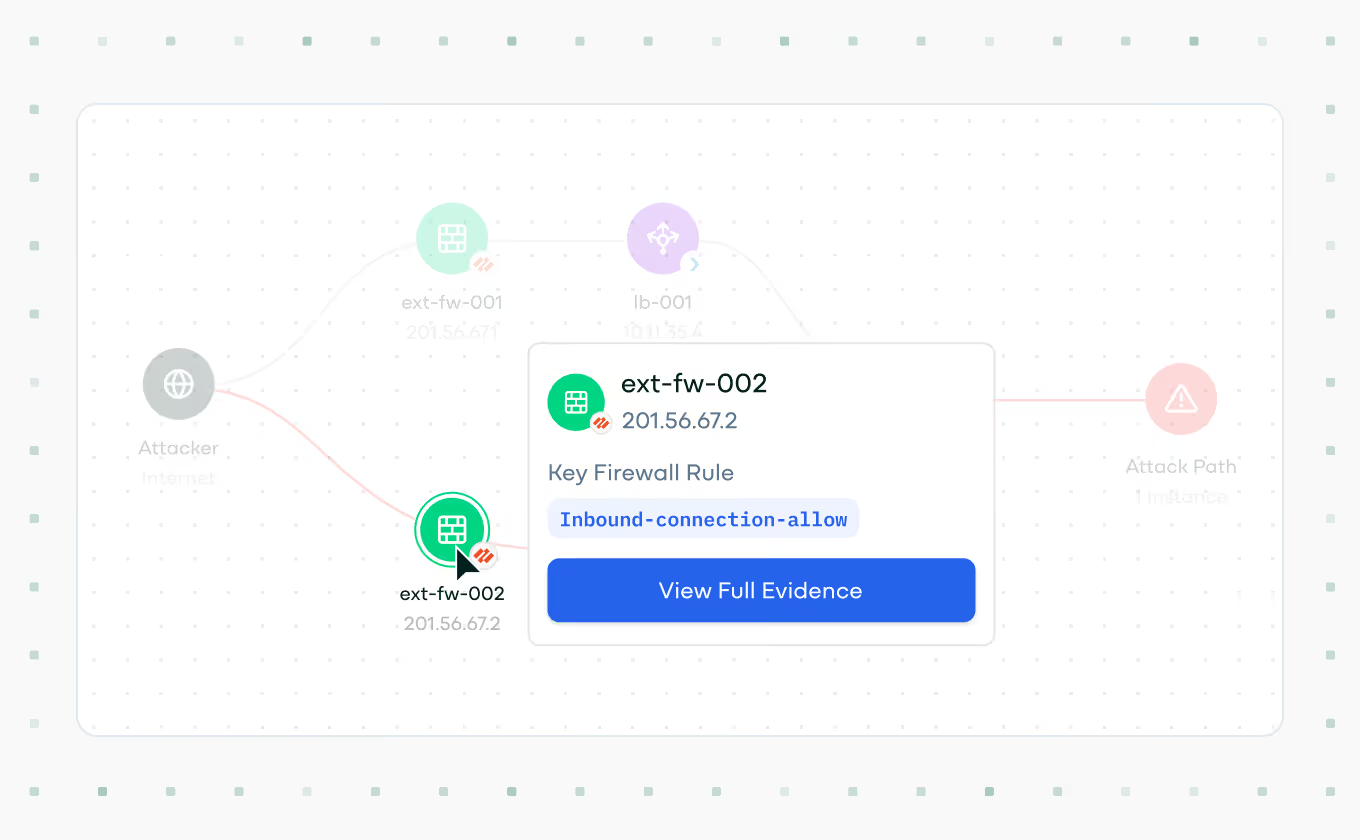
Understand exactly how an attacker can traverse your network to compromise vulnerable hosts, through graph-based representations.
Astelia highlights vulnerabilities that create real attack paths, visualizing how threats move through your network to reach and compromise critical assets.

With graph-based representations and environment-specific context, Astelia shows exactly how and why a vulnerability is exploitable, based on proof such as active processes and internet-facing exposure.
By identifying vulnerabilities on exposed hosts running exploitable services, Astelia ensures teams focus on threats that attackers can actually reach and exploit.
