In a recent research, Gartner® makes an important and long overdue point: “Cybersecurity leaders can materially reduce breach likelihood by prioritizing exposures based on real-world exploit activity, business criticality, exploitability likelihood and control effectiveness, rather than relying solely on severity scores” (Prioritize What Attackers Will Exploit: 4 Elements of Strong Exposure Prioritization, Jonathan Nunez, Gartner, March 2026).
I like the direction here. It aligns with what security teams experience every day. There is an overwhelming volume of exposures, and a CVSS-first workflow does not map cleanly to how attackers actually operate.
Where I want to build on this discussion is the element of security control integration and passive validation, which includes network reachability and segmentation. While it may appear as one component among several, in our experience at Astelia, the combination of reachability and exploitability is what turns the other inputs into action. It is the layer that answers the decisive question of whether an attacker can realistically reach and exploit a given asset in a specific environment at a given moment.
Reachability is the translation layer
A practical observation is that many of the commonly used inputs for prioritization are becoming increasingly commoditized. Threat intelligence feeds, exploit maturity indicators, probability signals, and general asset metadata are widely available and useful. However, they are no longer where most programs fail. The failure happens when teams cannot translate those global signals into local truth, meaning what actually matters in their own environment.
That translation is what reachability analysis provides.
Across discussions with defenders and research into attacker behavior, reachability is not optional. If an asset is not reachable from an attacker’s current position, whether external or from a compromised foothold, then even a severe vulnerability has limited practical impact. If it is reachable, even a low-profile issue can become critical.
Evaluating exposures in the context of existing controls such as segmentation, authentication requirements, endpoint protection, and detection coverage helps avoid misjudging risk. Reachability is the measurable layer beneath those controls.
Attackers don't read your backlog
Attackers operate with incomplete information. They begin with what they can access, then probe and expand. Each successful step reveals additional reachable assets.
The key question from an attacker perspective is whether something is accessible. Once access exists, attackers can often construct a viable path by chaining weaknesses, abusing identity, or investing effort into a targeted technique.
In one red-team engagement, a single reachable server acted as the only entry point into an environment. There was no ready exploit. However, because it was reachable, it became the focal point. The team invested time and eventually created a path forward, driven entirely by that initial accessibility.
Reachability shapes attacker behavior. It should also shape defensive prioritization.
The two conditions for exploitation
For vulnerability-driven compromise, two conditions are generally required:
- Reachability, meaning the ability to interact with the target from an attacker foothold
- A method to attack, such as an exploit, misconfiguration, credential path, or chainable weakness
If reachability is missing, the attack path is effectively blocked. If the method is missing, attackers may still develop one, particularly for high-value or uniquely accessible targets. This makes reachability a critical driver of risk.
Signals such as exploitability modeling and threat intelligence become significantly more useful when filtered through reachability.
Exposure prioritization matrix
A simple operational model is a 2×2 classification:
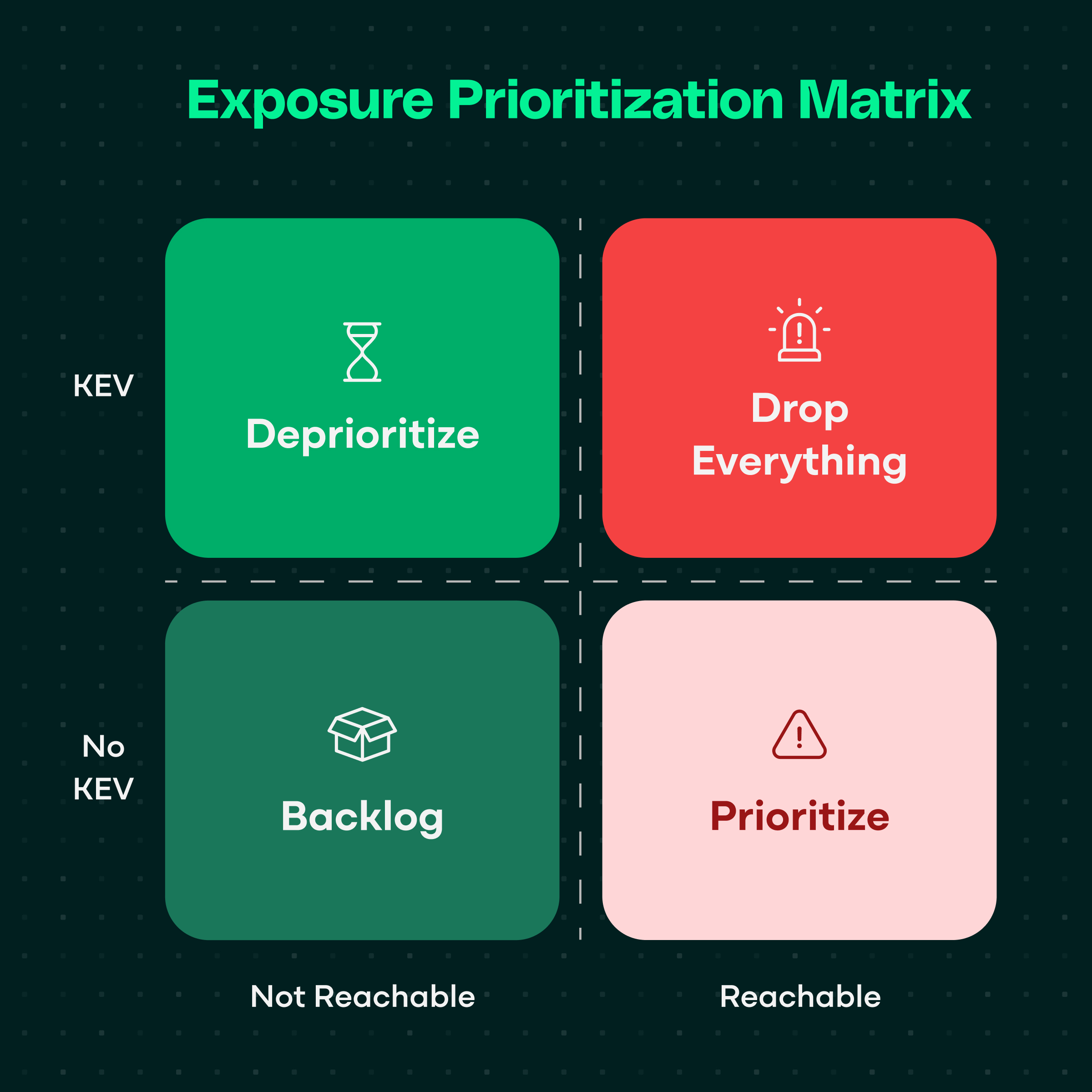
- Reachable and KEV (Known Exploited Vulnerability) → Drop everything
This represents an active and validated attack path. Immediate remediation or mitigation is required. - Reachable and No KEV → Prioritize
This is where proactive programs are effective. Addressing reachable issues before widespread exploitation is crucial for minimizing exposure. - Not reachable and KEV → Deprioritize
If reachability is confidently ruled out, risk may be mitigated by existing controls. This allows teams to avoid unnecessary work. - Not reachable and no KEV → Backlog
These items can be addressed through standard patch cycles or compensating controls, depending on asset context.
This approach does not replace other prioritization elements. It enables them to be applied effectively.
Why reachability is under-emphasized
Despite its value, reachability is not widely implemented because it is difficult to calculate across hybrid environments, cloud architectures, Kubernetes, firewalls, identity layers, and service meshes. Manual validation does not scale, so many teams deprioritize it.
However, this difficulty is also what makes it valuable. Reachability is a foundational component of attack path analysis. Understanding paths allows teams to focus remediation on what materially reduces exposure.
The backlog reduction payoff
Incorporating reachability leads to two consistent outcomes:
- Visibility into gaps, such as internet-facing assets that are not being scanned
- Significant reduction in noise by focusing on practical exposure rather than theoretical risk
In practice, reachability-driven prioritization can reduce critical vulnerability backlogs by 95 to 98 percent in some environments by filtering out exposures that are not exploitable in context.
This aligns with Gartner’s conclusion that “Success should be measured not by the number of vulnerabilities closed, but by reduction in exploitable exposures” (Prioritize What Attackers Will Exploit: 4 Elements of Strong Exposure Prioritization, Jonathan Nunez, Gartner, March 2026).
Defensible prioritization at scale
The foundational elements of exposure prioritization are important and should be present in any modern program.
However, prioritizing what attackers will exploit in a specific environment requires translating global signals into local reality. That translation layer is reachability and passive validation.
For teams early in this journey, the recommendation is straightforward. Maintain the foundational elements, but add reachability as a core requirement. Not as a checkbox, but as the mechanism that makes prioritization defensible, scalable, and aligned with real attacker behavior.
GARTNER is a trademark of Gartner, Inc. and its affiliates.


.jpg)









